Designs, Codes and Cryptography ( IF 1.4 ) Pub Date : 2024-08-10 , DOI: 10.1007/s10623-024-01473-z Shi Bai , Hansraj Jangir , Tran Ngo , William Youmans
|
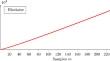
We describe a heuristic polynomial-time algorithm for breaking the NTRU problem with multiple keys when given a sufficient number of ring samples. Following the linearization approach of the Arora-Ge algorithm (ICALP ’11), our algorithm constructs a system of linear equations using the public keys. Our main contribution is a kernel reduction technique that extracts the secret vector from a linear space of rank n, where n is the degree of the ring in which NTRU is defined. Compared to the algorithm of Kim-Lee (Designs, Codes and Cryptography, ’23), our algorithm does not require prior knowledge of the Hamming weight of the secret keys. Our algorithm is based on some plausible heuristics. We demonstrate experiments and show that the algorithm works quite well in practice, with close to cryptographic parameters.
中文翻译:

一种用多个密钥破解 NTRU 的代数算法
我们描述了一种启发式多项式时间算法,用于在给定足够数量的环样本时用多个密钥来解决 NTRU 问题。遵循 Arora-Ge 算法 ( ICALP '11 ) 的线性化方法,我们的算法使用公钥构建线性方程组。我们的主要贡献是一种核缩减技术,该技术从等级为n的线性空间中提取秘密向量,其中n是定义 NTRU 的环的度数。与 Kim-Lee 的算法(设计、代码和密码学,'23 )相比,我们的算法不需要事先了解密钥的汉明权重。我们的算法基于一些合理的启发式方法。我们演示了实验并表明该算法在实践中效果很好,具有接近密码学的参数。
























 京公网安备 11010802027423号
京公网安备 11010802027423号